Incident Response Planning & Tracking
Incident Management
Software
Create your incident response plan and track incidents
Put your organization ahead of the curve by creating a plan for handling incidents. When an incident occurs, track and document your detection, response, and recovery processes using features based on guidance from the National Institute of Standards and Technology (NIST SP 800-61).
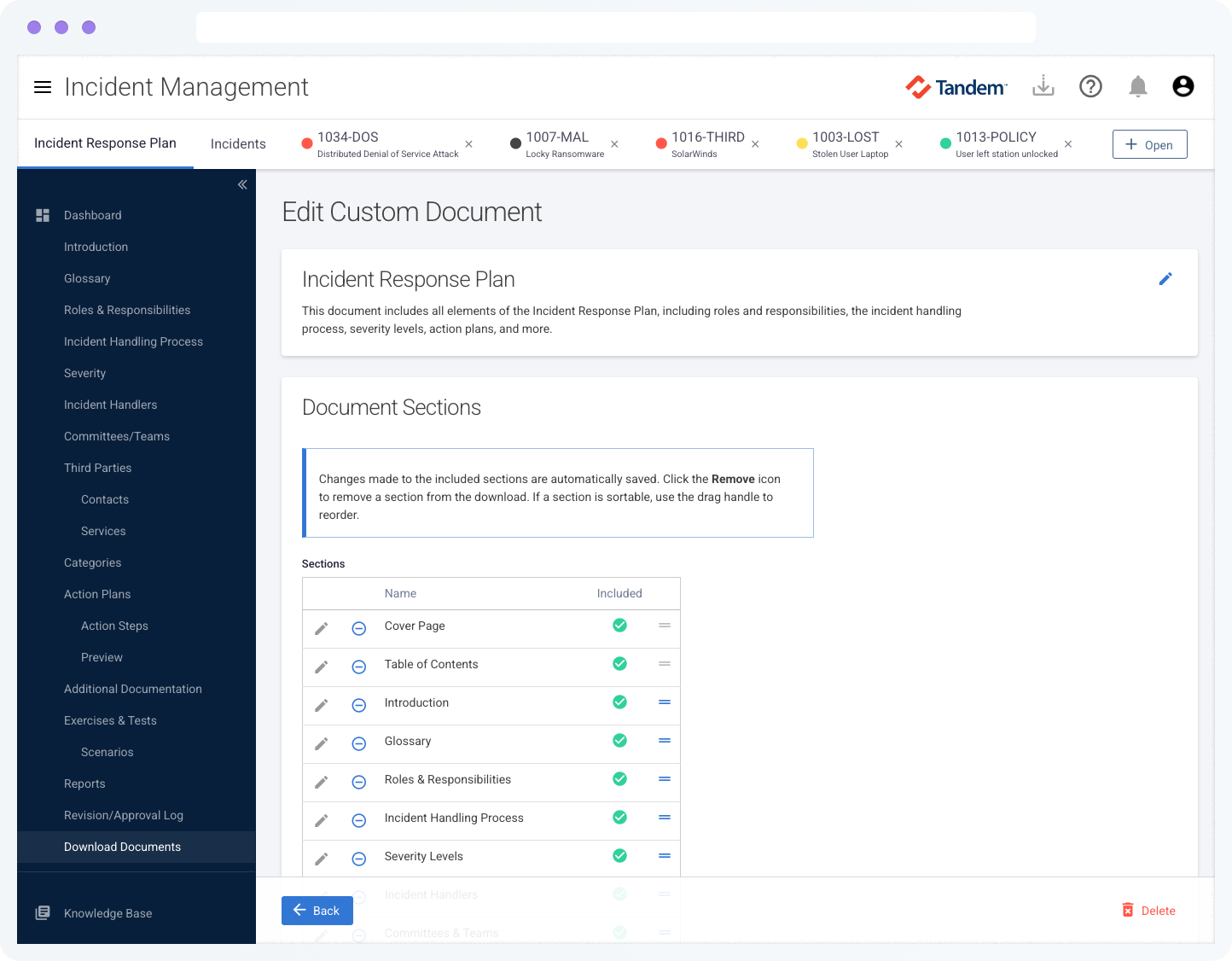
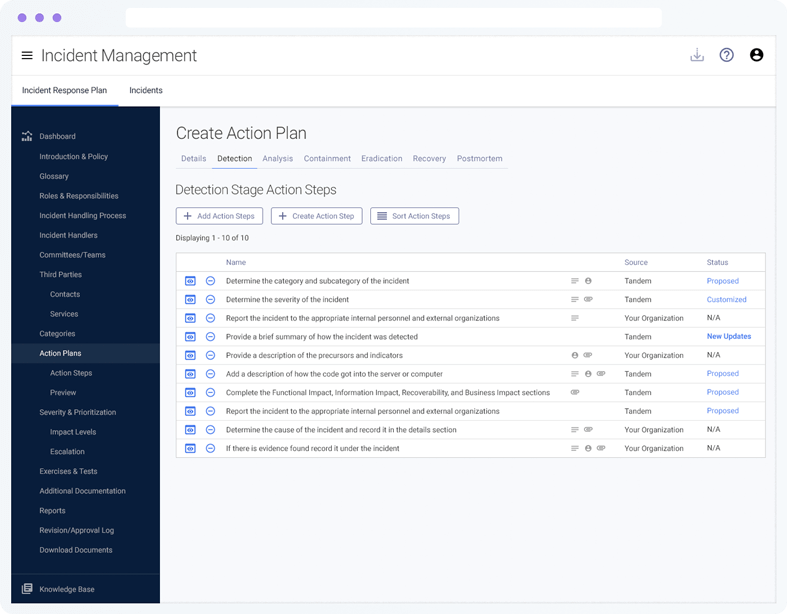
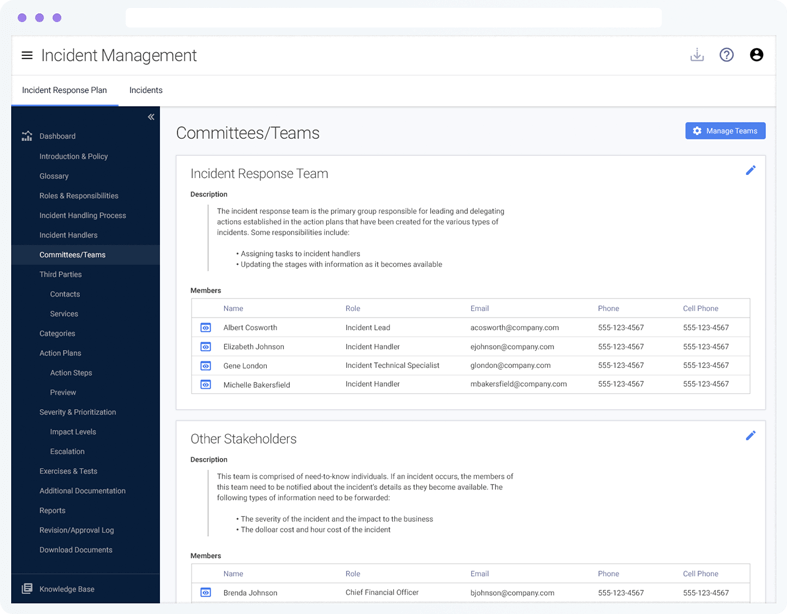
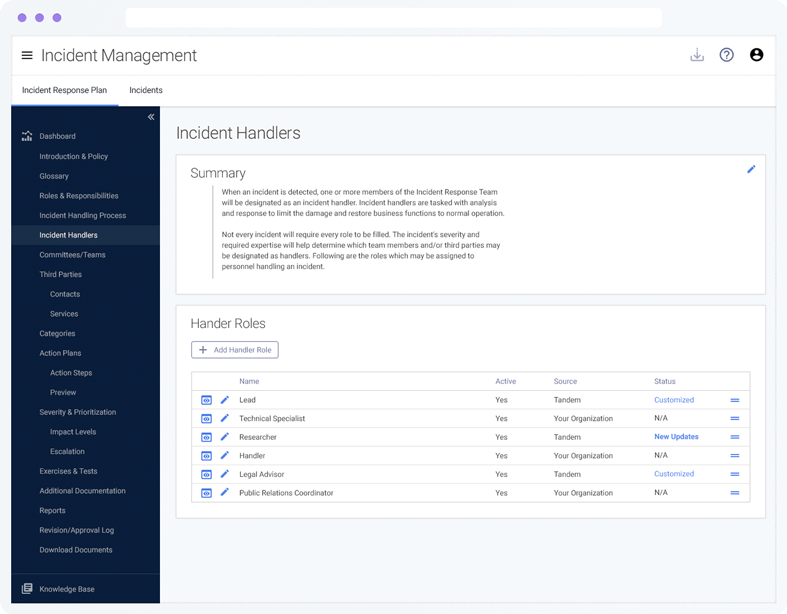
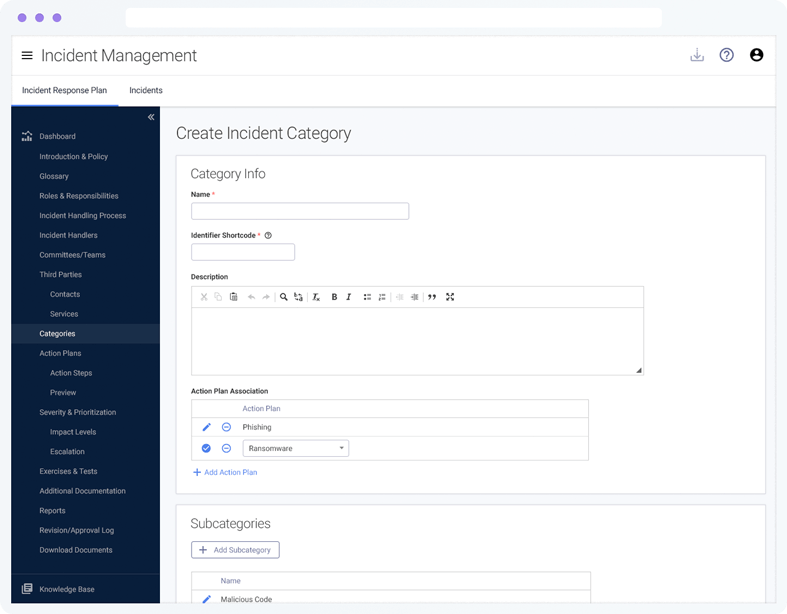
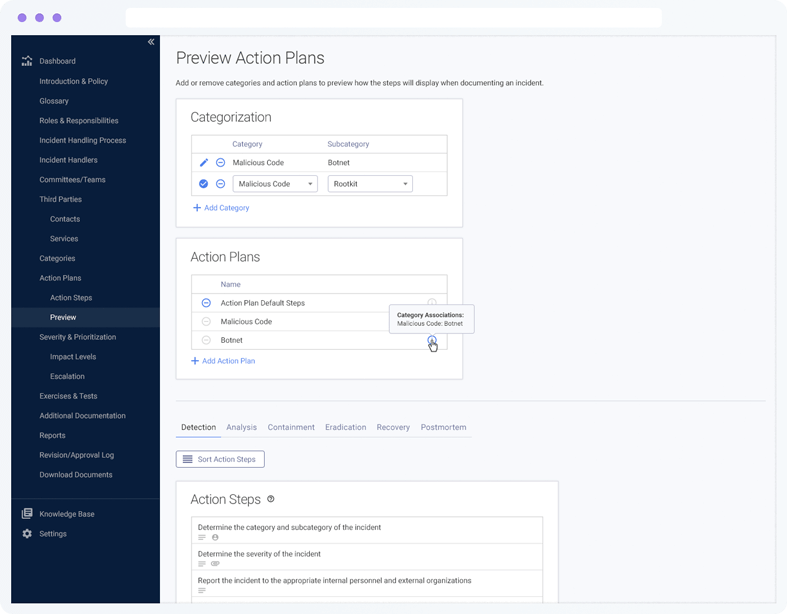
Incident Response Plan
Easily create and manage your incident response plan with built-in guidance, suggested wording, and helpful features to support you. Customize the plan to fit your organization by defining communication guidelines, assigning roles and responsibilities, building action plans for different types of incidents, and more.
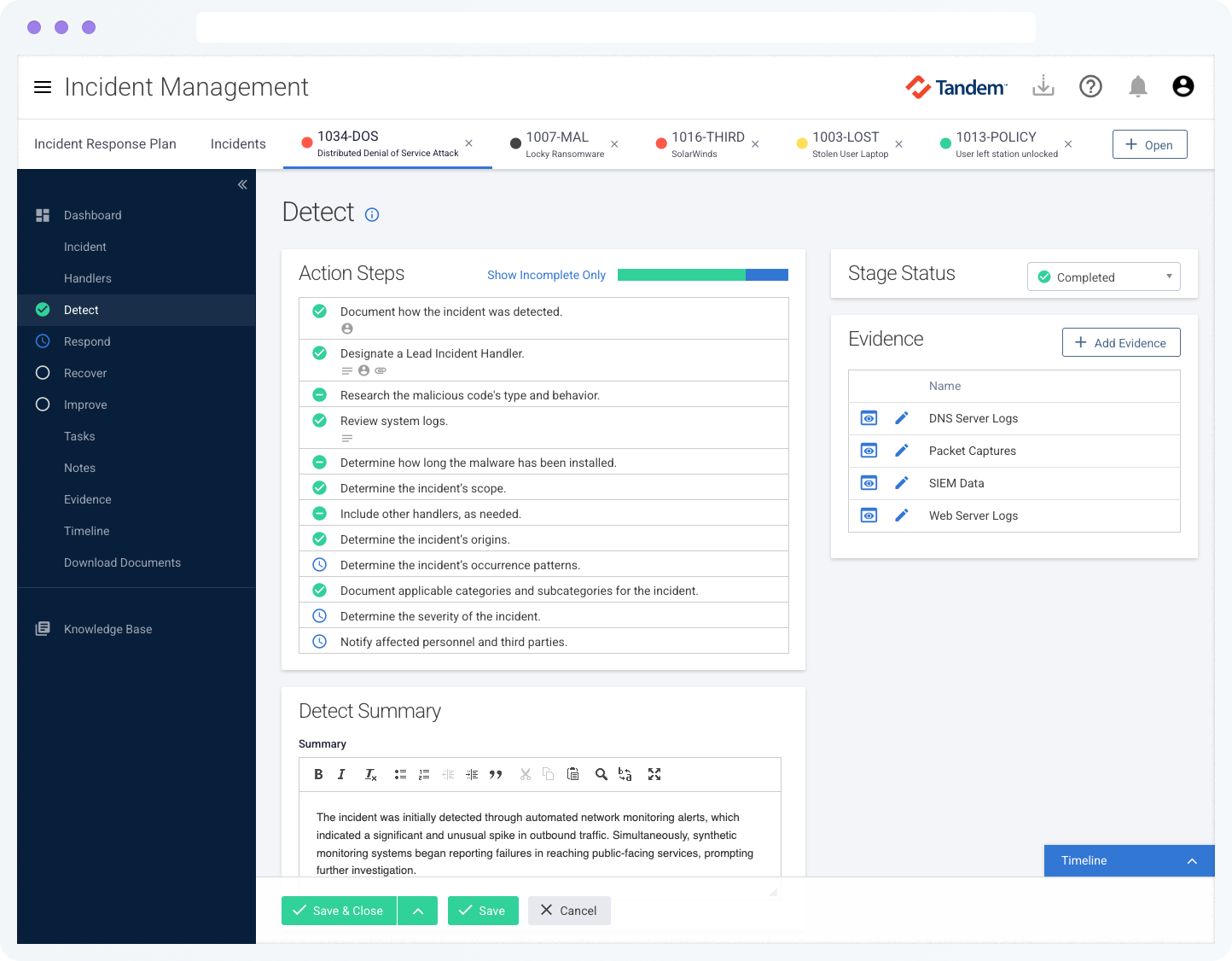
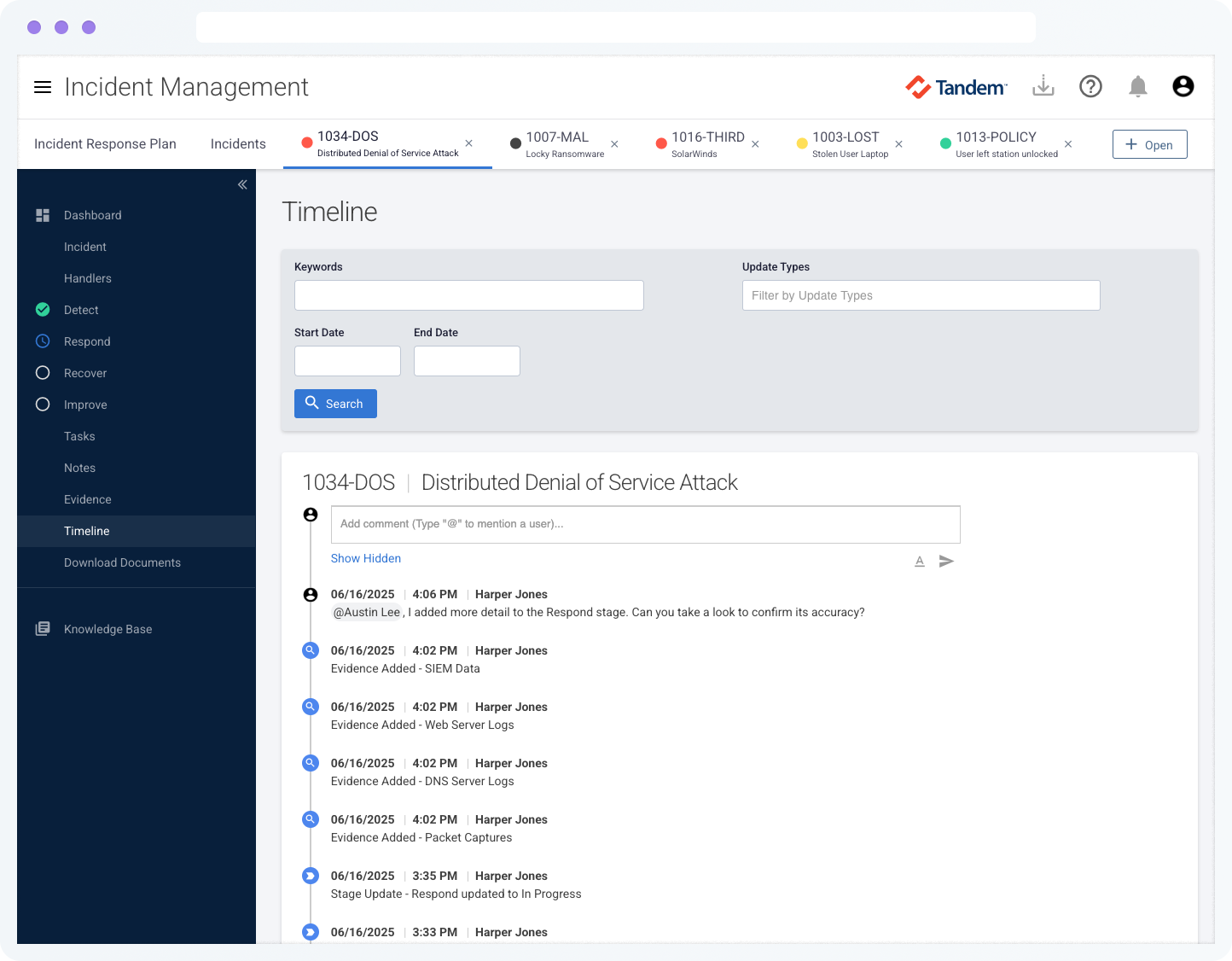
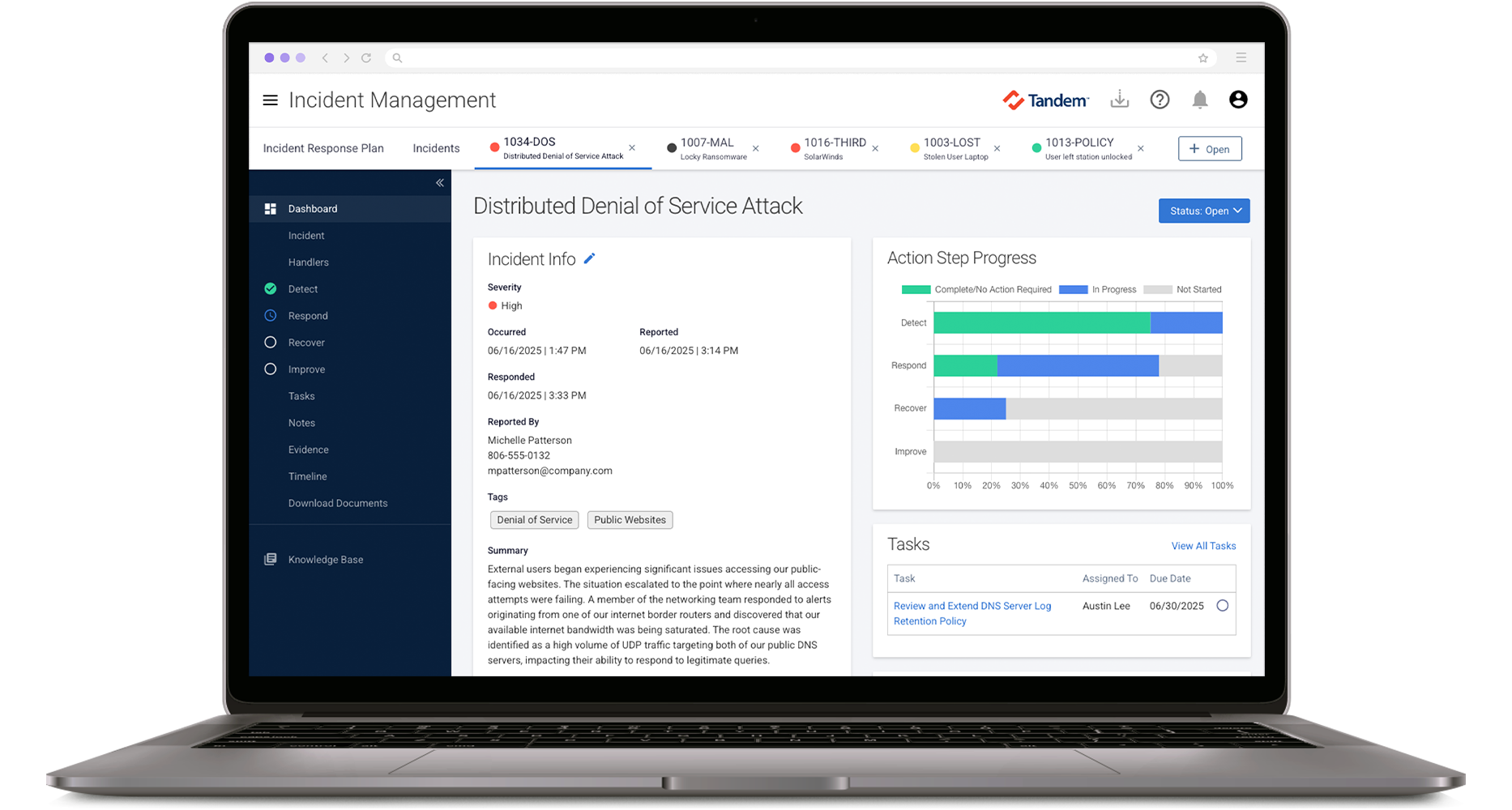
Tracking & Documenting
When an incident occurs, use the tracking component to document what happens at each stage. Built around the NIST process (Detect, Respond, and Recover), the tracking features make it easy to capture key details, learn from the incident, and improve your plan based on lessons learned.
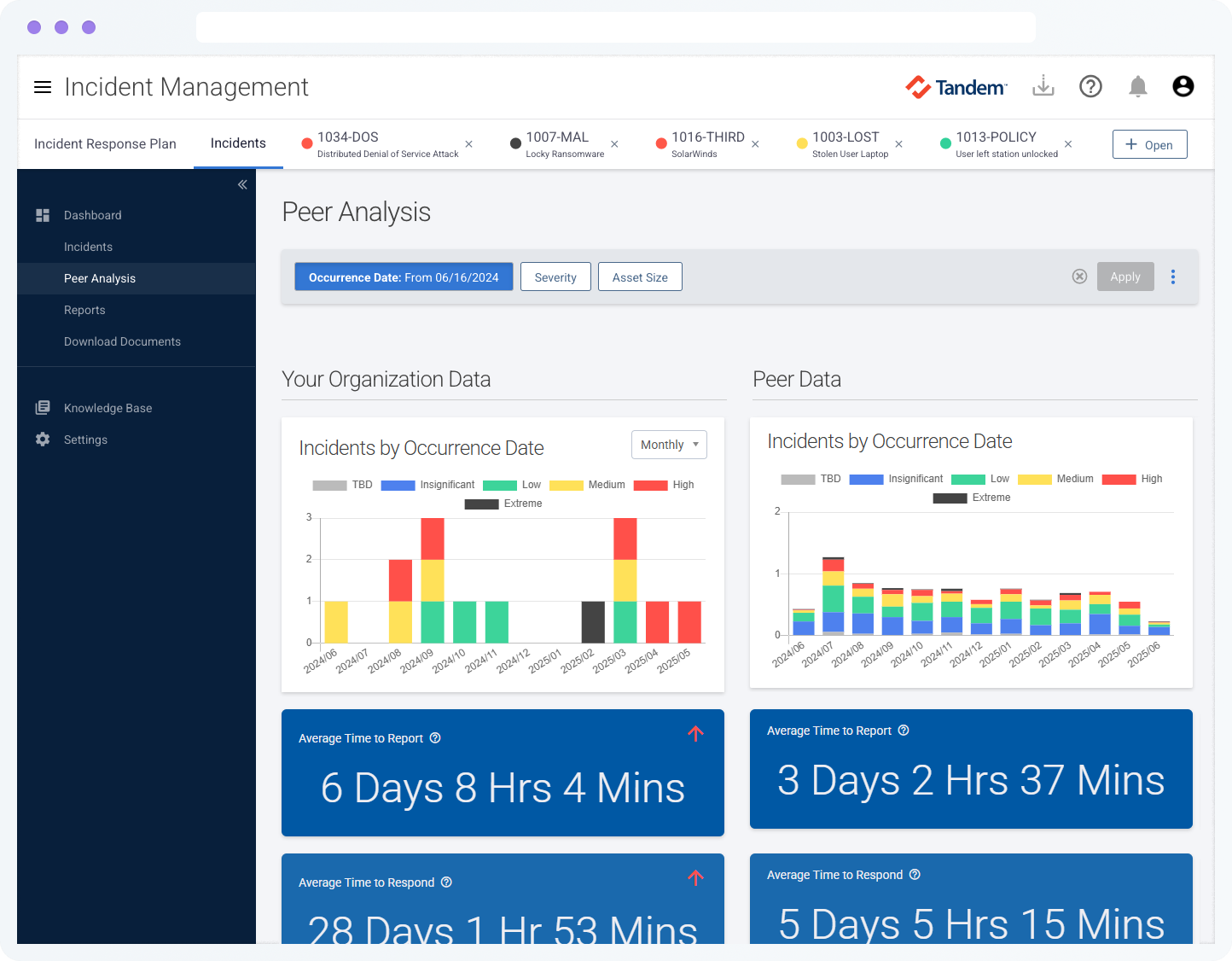
Peer Analysis
Gain perspective into your incident response processes by anonymously comparing your results with more than 350 other organizations who are tracking incidents with Tandem.
Additional Features
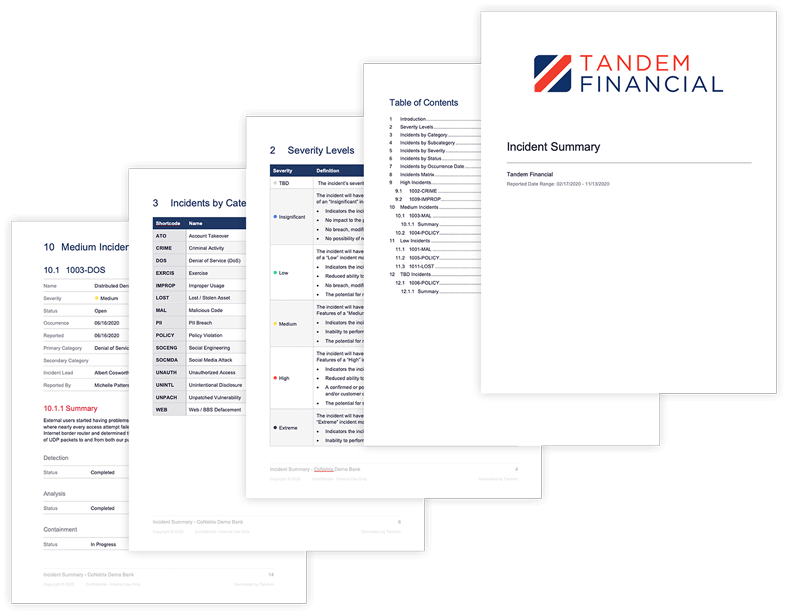
- Use global reporting to generate standardized documents
- Start with template incident response plan text and customize it to make it your own
- Specify roles and responsibilities for incident response within your organization
- Assign access roles like admin, edit, view only, or incident reporter
- Configure important notifications for incident handlers
- Store third-party contact information to improve incident communications
- Create custom sections for your incident response plan document
- Define terms used in your incident response plan with a built-in glossary
- Track an unlimited number of incidents
- Document the chain-of-custody for evidence related to incidents
- Create incident handling tasks, assign them to users, and monitor their status
- Run reports to identify gaps in your incident handling
Frequently Asked Questions
Yes. Tandem provides template language in the software that we call "suggested content." You can use our suggested content as a starting point, and quickly adapt the language to fit your company's unique requirements. Our suggested content is based on NIST Special Publication 800-61 and other industry guidance.
Tandem's suggested content is built and maintained by security and compliance experts who perform information security consulting services for financial institutions and other organizations with high security requirements.
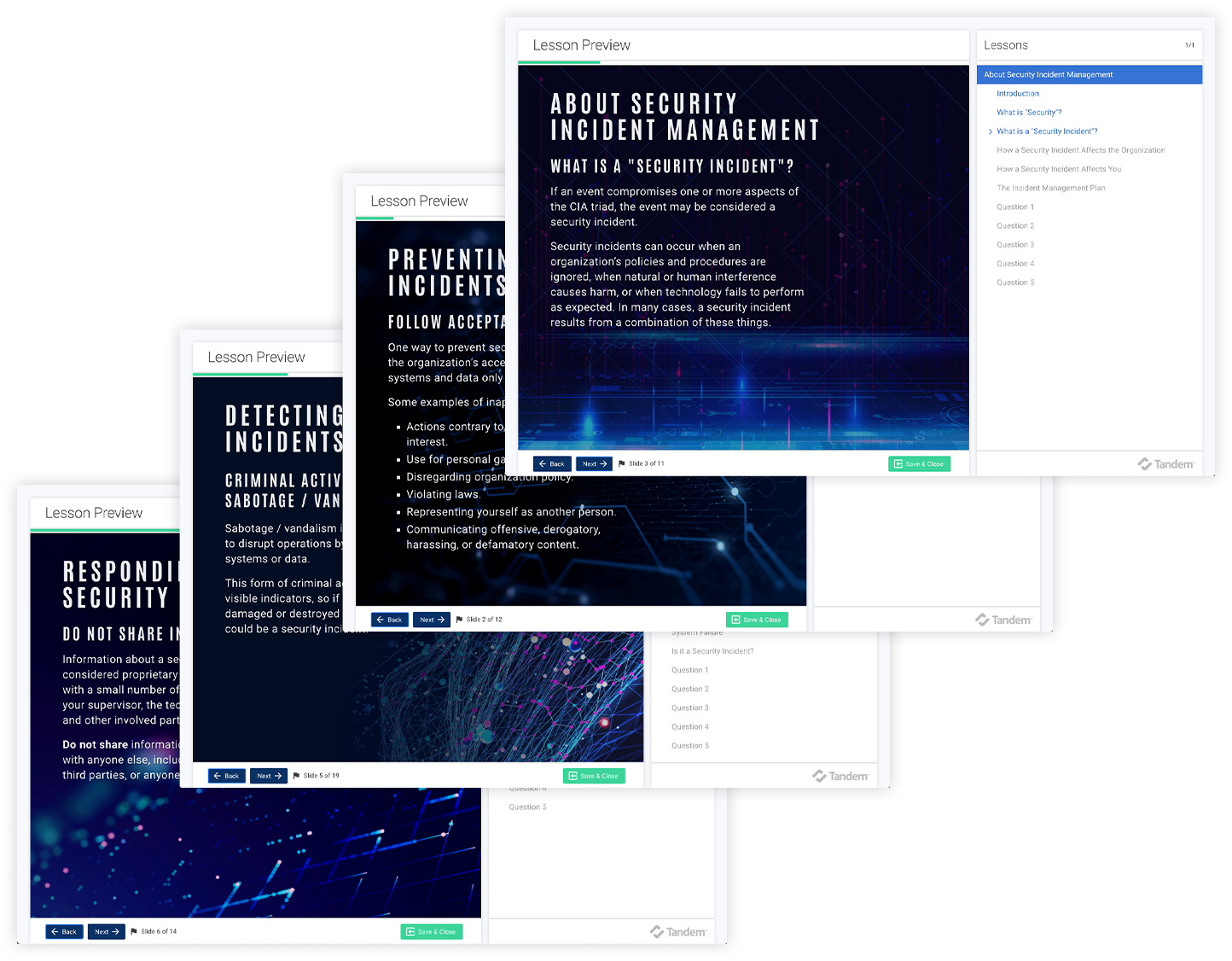
Yes. Tandem offers a Knowledge Base with articles written by Tandem experts. While you navigate the product you will also find help tips along the way.
The peer analysis feature uses anonymous, aggregated data to show how your incident metrics compare to other members of the Tandem community. It includes insights like incidents by date, severity, and average response time. You can opt in or out of participating in the anonymous peer data set at any time.
Yes. Tandem Support is available 8:00 AM – 5:00 PM (CT), Monday through Friday to answer your questions about Tandem application features.
For help with establishing or executing your incident management program, check out our partners who can provide incident management consulting.
You are also invited to attend our annual KEYS Conference to connect with other users and learn from Tandem experts.
Tandem is pleased to offer complimentary training webinars each month for our customers. These webinars are recorded and available on-demand.
A Knowledge Base is available with articles to help you learn about Tandem. You can stay up to date on our latest features by subscribing to our Software Update emails.
Product training is also available by request for an additional fee.
Yes. Tandem maintains high marks through the following testing: SSAE 18 SOC 1 Type 2, internal audits and assessments, quarterly penetration tests.
Security controls include:
- Secure data transmission between your browser and your servers
- Data encrypted at rest using AES-256
- User passwords are hashed and salted
- Datacenter protected by firewall and intrusion detection/prevention systems (IDS/IPS)
- Redundant internet connections
- Multifactor authentication options
- Single Sign On (SSO) integration using SAML 2.0
- IP address restrictions
- User activity log
- User access roles/restrictions
Tandem products are delivered via the internet as Software-as-a-Service (SaaS) applications. Tandem can be accessed from any device with a modern web browser. No software installation or special equipment is required.
New features and updates are included with your annual subscription and are automatically available. Each new feature is documented in our Software Updates blog.
Yes. Tandem Incident Management features integrate with Business Continuity Planning, Vendor Management, Risk Assessment, and Policies, to provide seamless sharing of data and help avoid duplication of information.
All Tandem products are available under the same secure website.
Yes. With a single login you can manage several companies' Incident Response Plans (requires a subscription for each company).